Cybersecurity Neural Sync – Obsidian Red-Team
Source Code Locked
Get the appropriate Subscription to unlock all copy-paste ready components instantly.
Description
Let us look at the Cybersecurity Neural Sync Obsidian Red Team component. This basic UI asset offers a modular card system specifically engineered for the cyber security sector. We built this entirely from scratch to handle heavy threat intelligence data without the usual framework bloat. You get a sterile DOM structure that fits right into your current security dashboard architecture.
Security platforms process massive amounts of live telemetry and require instant render times during active incident response. Heavy client side payloads completely ruin performance metrics in these critical scenarios. This component solves that bottleneck directly. By strictly avoiding external libraries like Tailwind, Bootstrap, or GSAP, it keeps your bundle size minimal. This ensures rapid rendering for security analysts and red team operators who need to monitor active network intrusions.
Technical Architecture & Performance
-
Zero dependency codebase: Built strictly with pure HTML, CSS, and Vanilla JavaScript to keep your front end stack incredibly light.
-
Guaranteed performance metrics: Optimized to help your security application maintain 90 plus PageSpeed scores and pass Core Web Vitals easily.
-
Safely scoped CSS: All styling is strictly scoped to prevent any class name collisions when you drop these cards into a massive monolithic repository.
-
Sterile DOM markup: Features clean HTML with absolutely no unnecessary wrappers or deep nesting trees to parse.
Design & Aesthetic Impact
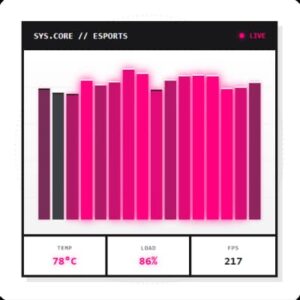
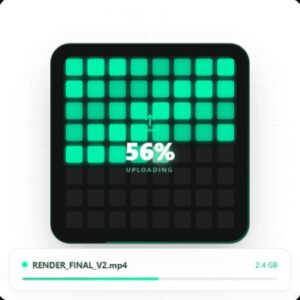
The visual direction pairs dark Obsidian Glass tones with a transparent aesthetic to establish absolute focus during intense threat assessments. This stark and highly readable approach ensures visual clarity for users analyzing complex cryptographic data and active firewall logs. For the interaction layer, we implemented custom orbiting node animations that act like small satellites. These continuous circular transitions provide clear visual feedback for live neural syncs and active network connections without requiring heavy javascript animation scripts. The final result is a highly polished user interface that looks premium and functions perfectly for strict security operations centers.
Enterprise Use Cases
-
Threat intelligence dashboards: Display live vulnerability scans and satellite node connections using the card grid so security teams can monitor threat vectors quickly.
-
Incident response portals: Build a fast rendering alert page where network administrators can organize and review massive datasets of unauthorized access attempts within a lightweight interface.
-
Red team audit panels: Create a responsive control layout for penetration testers to track active network syncs and payload deployments across multiple client systems.
Highlights & Benefits
Drop the code straight into your project without configuration.
Built strictly with pure CSS & Vanilla JS for maximum speed.
Constructed with strict adherence to WCAG accessibility standards for perfect contrast and screen-reader support.
Utilizes a highly optimized, clean DOM architecture ensuring lightning-fast render and maximum PageSpeed scores.

Cybersecurity Neural Sync – Obsidian Red-Team
Description
Let us look at the Cybersecurity Neural Sync Obsidian Red Team component. This basic UI asset offers a modular card system specifically engineered for the cyber security sector. We built this entirely from scratch to handle heavy threat intelligence data without the usual framework bloat. You get a sterile DOM structure that fits right into your current security dashboard architecture.
Security platforms process massive amounts of live telemetry and require instant render times during active incident response. Heavy client side payloads completely ruin performance metrics in these critical scenarios. This component solves that bottleneck directly. By strictly avoiding external libraries like Tailwind, Bootstrap, or GSAP, it keeps your bundle size minimal. This ensures rapid rendering for security analysts and red team operators who need to monitor active network intrusions.
Technical Architecture & Performance
-
Zero dependency codebase: Built strictly with pure HTML, CSS, and Vanilla JavaScript to keep your front end stack incredibly light.
-
Guaranteed performance metrics: Optimized to help your security application maintain 90 plus PageSpeed scores and pass Core Web Vitals easily.
-
Safely scoped CSS: All styling is strictly scoped to prevent any class name collisions when you drop these cards into a massive monolithic repository.
-
Sterile DOM markup: Features clean HTML with absolutely no unnecessary wrappers or deep nesting trees to parse.
Design & Aesthetic Impact
The visual direction pairs dark Obsidian Glass tones with a transparent aesthetic to establish absolute focus during intense threat assessments. This stark and highly readable approach ensures visual clarity for users analyzing complex cryptographic data and active firewall logs. For the interaction layer, we implemented custom orbiting node animations that act like small satellites. These continuous circular transitions provide clear visual feedback for live neural syncs and active network connections without requiring heavy javascript animation scripts. The final result is a highly polished user interface that looks premium and functions perfectly for strict security operations centers.
Enterprise Use Cases
-
Threat intelligence dashboards: Display live vulnerability scans and satellite node connections using the card grid so security teams can monitor threat vectors quickly.
-
Incident response portals: Build a fast rendering alert page where network administrators can organize and review massive datasets of unauthorized access attempts within a lightweight interface.
-
Red team audit panels: Create a responsive control layout for penetration testers to track active network syncs and payload deployments across multiple client systems.